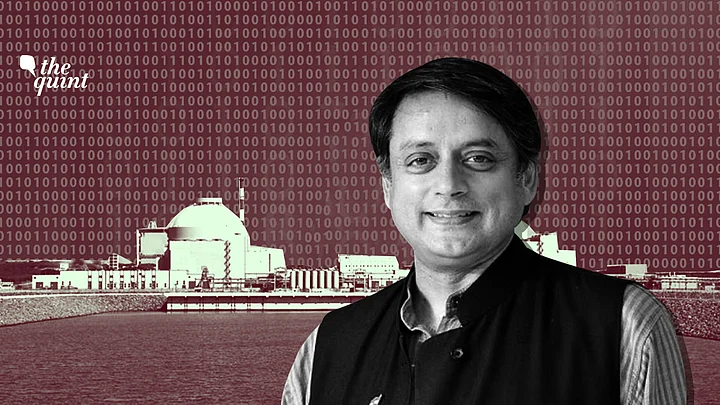
The National Power Corporation of India Ltd’s (NPCIL) admission that its “systems” at the Kudankulam nuclear power plant were breached by a malware attack in September does little to assuage public concerns about the government’s lax approach to cyber-security. NPCIL tried to assure the public that no critical systems were compromised, and the malware only hit an “administrative” network. But this is the administration of a nuclear plant!
Despite proclamations of a ‘Digital India’ by Prime Minister Narendra Modi and his government, very little has been done on the ground to secure the systems and networks upon which the country’s digital economy stands.
If anything, the statement raises more questions than it answers: how did the malware enter the plant’s physical premises, and into the digital infrastructure of an “air-gapped” — isolated from the ‘civilian’ internet — network? Did it really target the Kudankulam plant, or was this “infection” the residual aftereffect of another sophisticated cyber attack?
For example, the Stuxnet worm took aim at the Iranian nuclear infrastructure, but ended up in many industrial command-and-control systems supplied by Siemens, including to Indian corporations. Might this have happened to us again?
Disruptive activity in cyberspace is today cheap to execute and costly to prevent or repel.
Govt Has To Answer These Critical Questions
- If an Indian strategic installation such as Kudankulam was the intended target, what information was compromised?
- It is not enough to say that the infected system was used for “administrative purposes” — did this system bear information such as passwords or confidential correspondence that could pave the way for a more intrusive attack?
- And finally, what does the government plan to do to mitigate damage from this incident and prevent future cyber attacks?
Pursuant to Section 70A of the Information Technology Act, 2000, the Indian government can notify certain strategic installations as “Critical Information Infrastructure” and accordingly, ring-fence them from digital intrusions. The nodal agency for this purpose is the National Critical Information Infrastructure Protection Centre (NCIIPC).
In 2017, the then Minister for Power, Coal, New and Renewable Energy, Piyush Goyal, even declared in Parliament that the NCIIPC had “taken several steps to sensitise power utilities and key stakeholders against cyber threats”. Would the government now care to address what these steps were?
The unfortunate reality is that, despite proclamations of a ‘Digital India’ by Prime Minister Narendra Modi and his government, very little has been done on the ground to secure the systems and networks upon which the country’s digital economy stands.
The country’s national security architecture must be nimble in its decision-making processes and accommodating in its recruitment procedures.
The National Cybersecurity Policy formulated in 2013 by the United Progressive Alliance-II has been overtaken by the sheer scale and speed of change in digital innovation. Disruptive activity in cyberspace is today cheap to execute and costly to prevent or repel. Yet, there has been no attempt to revise this strategy to meet contemporary challenges.
Where is India’s National Security Doctrine?
A national security doctrine has been in the works for a long time like the mythical khichdi of Birbal, as has been the creation of a Defence Cyber Agency. The DCA was reportedly set up this summer, but beyond speculations in the press, no one knows if it actually exists!.
It is unclear what the thrust of either the doctrine or the DCA will be, because the Modi government is itself ambivalent and rudderless in its approach towards India’s strategic objectives. The cyber intrusion on Kudankulam is a perfect example: it may reportedly be the handiwork of the North Korea-based Lazarus Group. But what if this group or other cyber mercenaries are merely proxies for India’s bigger and more powerful adversaries like China and Pakistan?
It is all very well to call for restraint, but New Delhi should keep the proverbial gunpowder dry.
The piecemeal, haphazard and all-too-bureaucratic way in which the government machinery has responded to the Kudankulam breach — first denying the incident altogether, followed by a qualified admission that “critical systems” are safe — ignores the larger motivations behind the attack.
Is India Doing Enough to Build Global Partnerships for Combating Cyber Threats?
The fortifying of India’s digital infrastructure has to be accompanied by diplomatic initiatives that nudge states towards restraint in cyberspace. While New Delhi was an active participant in the 2016-17 Group of Governmental Experts constituted to determine “rules of the road” for state conduct in cyberspace, the GGE itself disbanded without a consensus report.
The 2015 iteration of the GGE’s report had already urged states not to target the critical infrastructure of others, but enforcing this norm has proved a challenge. Starting December 2019, the GGE, reconstituted for a sixth time with a two-year life span, will attempt to identify how international law applies to the actions of states and non-state actors in cyberspace. India is a part of this group, and must use its good offices to secure a strong report that chastises the targeting of critical infrastructure like nuclear plants.
These norms, however, are of little value unless they are elevated into a binding international instrument, like the Convention on the Peaceful Uses of Outer Space. In particular, a multilateral institution that can effectively attribute cyber attacks of a regional or global nature will be essential to the success of such an instrument.
And finally, India must systematically build and consolidate its offensive cyber capabilities to deter and punish such serious intrusions. It is all very well to call for restraint, but New Delhi should keep the proverbial gunpowder dry. The old adage “if you want peace, prepare for war” applies to cyber warfare as well.
To their credit, various actors and institutions in India’s national security landscape recognise the need to enhance the country’s cyber capabilities. But their enthusiasm or initiative can only bear fruit if they receive encouragement and guidance from the very top. A lot will depend on the government’s ability to tap talent from the private sector — but to harness India’s considerable manpower in computer programming for strategic purposes, the country’s national security architecture must be nimble in its decision-making processes and accommodating in its recruitment procedures.
The Kudankulam security breach has set the alarm bells ringing for all those who worry about India’s cyber security. It is time for the government to spring to attention and take decisive steps to prevent the next breach.
(Former UN under-secretary-general, Shashi Tharoor is a Congress MP and an author. He can be reached @ShashiTharoor. This is an opinion piece and the views expressed above are the author’s own. The Quint neither endorses nor is responsible for the same.)