A fraudulent link, primarily circulated on WhatsApp, offers users a chance to win free gifts as part of a fake 'Amazon's Valentine's Day Campaign'.
CyberPeace Foundation and Autobot Infosec found that by clicking on the link and following the instructions on the page, your personal information could be stolen and a malware could be installed on your phone.
"If at all, a user gets into this trap, it could lead to the whole system being compromised, such as access to microphone, camera, text messages, contacts, pictures, videos, banking applications etc, as well as financial losses," the report said.
Since the scam encourages sending the link through WhatsApp to multiple contacts, it could have a widespread impact, says Vineet Kumar, founder of CyberPeace. "It could be in the millions," he says.
We are awaiting a comment from Amazon.
How the Scam Works
The WhatsApp link appears to offer "15,000 free products!" as Valentine's Day gifts from Amazon. Clicking on this will redirect you to a link which looks like https://tinyurl2[.]ru/m045130551 followed by a unique 13 digit number.
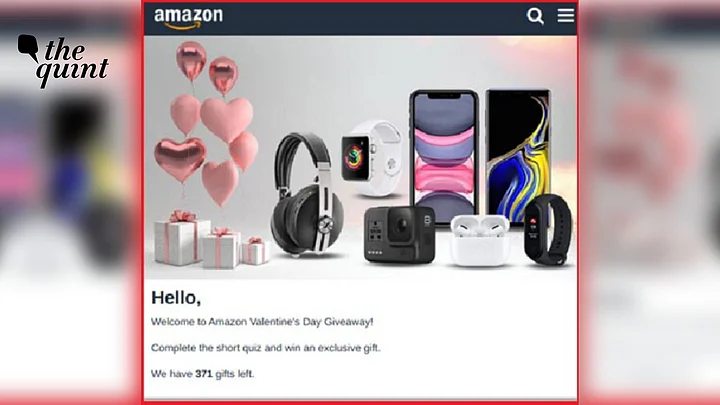
The landing page looks authentic, with an Amazon banner and a photograph of various electronics. The welcome message asks you to complete a short quiz to win an exclusive gift.
It even has a fake comments section at the bottom where users seem to affirm the legitimacy of the offer and share their positive experiences.
Once you answer a few basic questions (Do you know Amazon? How old are you?), a congratulatory message is displayed, after which users are given three attempts to win the prizes by randomly choosing gift boxes.
It will then tell you that you have won an "Apple iPhone 11 128GB" and ask you to share this campaign on WhatsApp.
The report noted that users have to click the WhatsApp button multiple times until the progress bar completes. After you finish your "registration", it will redirect you to multiple advertisement webpages.
What the Report Found
After conducting an in-depth investigation, CyberPeace made the following observations:
The scam seems to be focused on mobile users. If you open the link on desktop, you will see an error message.
The social media comments were static and are added to the page with HTML and CSS. The quiz, progress bar, and other features are also static.
Malware settrogens[.]com was being connected to in the background. It is widely used by attackers to compromise a user's browser and trigger malicious activities.
Encoded script embedded in the source code contained all the details about what type of data was to be stolen from the users. This includes browser and system information.
The cybercriminals used Cloudflare technologies to mask their real IP addresses. The domain name used has also been registered recently.
The report advised people to avoid clicking on any such links on social media platforms and refrain from sharing confidential details like banking information.
It also recommended that people don't share links without verifying them first.