A recent press conference in London was expected to demonstrate how the Electronic Voting Machines (EVM) can be hacked. What emerged, instead, was a cocktail of explosive but unsubstantiated claims.
In the context of the renewed political debate on EVMs that the conference has triggered, it is useful to go back nine years when the nation was stunned by a hack demonstrated on an actual EVM machine.
Hari K. Prasad, a Hyderabad-based engineer, who was arrested shortly after his demonstration, told The Quint that the EVM can be tampered with even today at various levels.
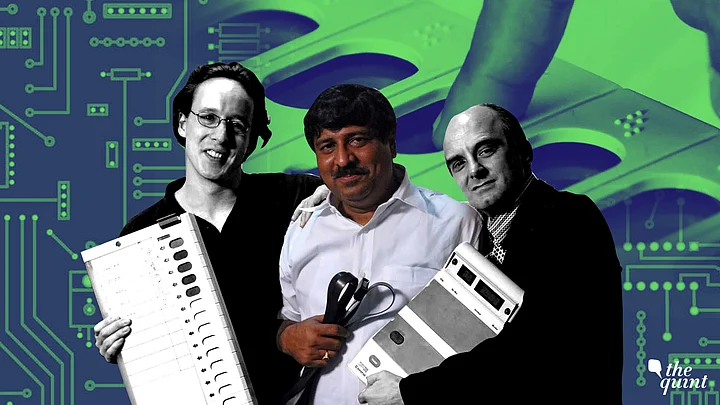
In 2010, Prasad, in collaboration with American computer scientist J. Alex Halderman, and Rop Gonggrijp, a Dutch hacker, had exhibited two different methods of tampering with the machine to manipulate the results.
He had demonstrated how the EVM could be physically tampered to favour a particular candidate as well as how a candidate’s votes can be stolen from the machine.
The Hack of 2010
So, what happened in the monsoon of 2010?
Prasad, who is currently technology advisor to the Govt. of Andhra Pradesh is also MD of Netindia Private Limited. In August 2010 he had received an actual EVM from an anonymous source. Upon his arrest on charges of theft , the police had claimed that the machine was stolen from a customs house in Mumbai where it was stored.
He collaborated with Halderman, a computer science professor at the University of Michigan, and Gonggrijp, a Dutch technology activist who was instrumental in having EVMs banned in the Netherlands. The three also published a paper on their case study in which they detailed the attacks they carried out on the EVM.
“We had got the EVM machine for just one day and carried out all our experiments in a short period of time. If we had more time we could’ve demonstrated more methods of hacking,” said Prasad.
The case study explains in detail the two methods employed to manipulate the EVM. Following are some important points about their case study.
- Their experiment was performed on a second generation EVM or M2. The current EVMs are M3.
- Both the hacks were carried out by physically manipulating the machine.
- The hack was carried out on an actual EVM and not upon a replica.
1. Favouring a Particular Candidate (Dishonest Display Attack)
To demonstrate how the EVM can be manipulated to favour a particular candidate, a dishonest display board was installed that can replace the real display board in the control unit.
Normally, when votes are counted, the EVM display board shows the number of votes received by each candidate. The dishonest display adds a separate, hidden micro controller that intercepts the vote totals and substitutes fraudulent results.
“Once the dishonest display is installed in an EVM (possibly months or years before the election), the attacker must communicate which candidate is to be favored (or disfavored), and by what margin,” the paper explains.
There are many different ways that attackers could send such a signal— with various kinds of radios, using secret combinations of key presses, or even by using the number of candidates on the ballot.
2. Stealing Votes (Memory Manipulator Attack)
Prasad implemented a second attack that demonstrates how malicious hardware can alter the internal state of the machine. Unlike the dishonest display attack, which involved replacing hardware components with look-alikes, this second attack involves only the temporary application of new hardware.
Any time between the start of polling and the public count, dishonest election insiders or other criminals could use a clip-on device that clips directly to the memory chips that record the votes inside the EVM to change the votes recorded in the EVM.
Another variation of this attack is an electronic version of the booth capture attack. To steal votes, the attacker indicates his favored candidate using the rotary switch and can use it to pick a favored candidate in any of the first nine ballot positions, which normally include the major national parties. When the switch is set to positions 1–9, the clip-on device executes a vote-stealing program.
‘Many Stages at Which EVM Can be Attacked Today’
Prasad said that while he was not convinced with the claims made by Syed Shuja at the London press conference, he nonetheless, is convinced that the EVM can be attacked and manipulated in various ways.
Into the Heart of the EVM
Prasad claims that at the heart of the potential vulnerability of EVMs is the fact that the main micro controller chip is manufactured outside India and hence it is practically impossible to find out if the chip itself has built-in vulnerabilities.
The Electronics Corporation of India Limited (ECIL), which designs the election software, ‘burns’ or fuses the program onto the chip on a one time programmable basis (OTP). According to an Expert Committee report on EVMs, this means that once fused, “it cannot read, copied out, altered and re-fed into the chip at all”
“The point is, because of the masked code, nobody can say with certainty that there cannot be built-in vulnerabilities in the chip design ,” said Prasad. “ Even if there is a vulnerability it will be impossible for the Election Commission to detect. So, how do you rule out that there cannot be another circuit designed within the chip?”
JT D’Souza, a technocrat who has researched extensively on voting security and EVMs corroborates Prasad’s claim. “Because the OTP does not allow the code to be scrutinised, it is not possible to find out if there was a trojan or other vulnerability.”
The EVM can be tampered with and manipulated with at the microcontroller chip level, at the memory level, at the motherboard level or even at the display level in the machine which displays the total number of votes cast. While these are hypothetical situations they are nonetheless realistic possibilities.Hari Prasad
Can It Be Attacked Remotely?
The first hack that Prasad and his collaborators had performed was the display attack. This method controlled the display remotely and wirelessly from a mobile phone using bluetooth radio signals.
The case study explains, “To demonstrate the potential for wireless signals, we implemented a signaling mechanism based on the Bluetooth radio protocol. Wireless signaling could be performed at any time before votes are publicly counted.”
What if ECIL sources its EVM display boards from a dishonest vendor which supplies the hackable display board that we inserted? The EC would not be able to find out. In that case, the bluetooth radio signals that we used remotely to change the display can be used by malicious people to manipulate candidate votes.”Hari Prasad
So, the question then is, to receive radio signals can one insert an antenna that is tiny enough to go undetected?
“For low frequency the antenna can be hidden within the circuit board,” he replied.
‘An Open EVM Architecture Better for Democracy’
All the security researchers that The Quint spoke with were united in their appeal for the architecture of EVMs to be kept open to ensure greater transparency.
Prasad feels that any hardware design in a democracy should be kept open. “If the EC truly wants to ensure that all the vulnerabilities in the EVM are detected are patched then the best way is to keep its architecture open.”
“If you look at the United States, they have the most advanced capabilities with agencies like the NSA. And yet they hand over the entire architecture of their EVMs at events like Defcon. They don’t need to but it increases transparency and accountability,” said Srinivas Kodali, a security researcher.
An 11-year-old called Emerett Brewer made headlines in August 2018 for successfully hacking into a an EVM replica at Defcon.
D’Souza agrees with this claim and stated “if anyone argues that an open EVM design is a security threat then that argument needs to be immediately discarded. There is no such evidence to prove it.”