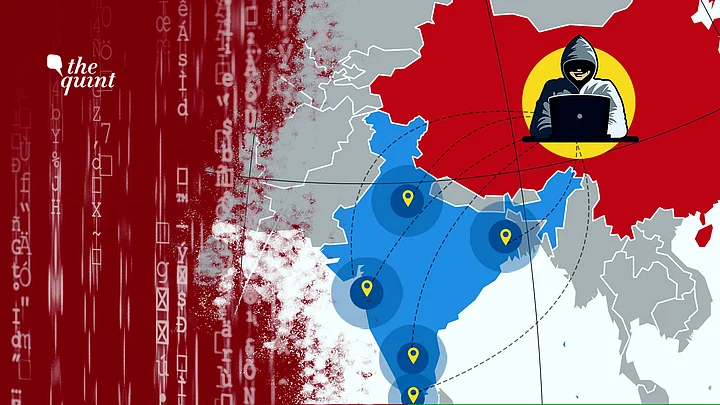
India is likely to see a rise in attacks throughout 2021 on its infrastructure and organisations by Chinese state-sponsored threat actor groups like Red Echo, US-based cybersecurity company Recorded Future said on Thursday, 4 March.
Amid the Indo-China conflict along the Line of Actual Control (LAC) in 2020, China-based threat actor group, codenamed ‘Red Echo’, had targted at least 10 assets of India’s critical power sector as well as two ports, a report by the company had stated.
All the twelve targeted entities have been classified as critical infrastructure by the National Critical Information Infrastructure Protection Centre (NCIIPC).
These include four out of five of India’s Regional Load Despatch Centres. They are responsible for ensuring real-time integrated operation of India’s power grid through balancing electricity supply and demand to maintain a stable grid frequency.
The targeted units, including Mumbai Port Trust, VO Chidambaranar Port in Tamil Nadu, are spread across different parts of India including Delhi, Maharashtra, Telangana, Karnataka, West Bengal and Assam.
Targeting of Civilian Infra ‘Concerning’: Cyber Firm CEO
“Targeting of important organisations in India by Chinese groups like Red Echo will likely continue in 2021,” the company stated during Thursday’s press conference.
Speaking at a press conference, Recorded Future CEO, Christopher Ahlberg described the selective targeting of India’s civiian infrastructure including power grids by the China-linked cyber group in 2020 as “ very unusual” and “concerning”.
He also clarified that they do not have sufficient data to substantiate that the power outage in 2020 was caused by Red Echo’s cyber attack.
While the Maharashtra government has launched an investigation into the matter, the Centre said that there has been no evidence of China’s role in the matter so far.
Govt Should Make Attacks Public to Deter Hackers: Cyber Firm CEO
He asserted the activities were not aimed at stealing money or information but more as, “A warning or show of force during heightened bilateral tensions.”
He advised the government to increase transparency around the threat activities by making any such malware attack public, as a way of deterring threat actors like Red Echo.
“Transparency is key here. Threat actors benefit from a lack of transparency,” Ahlberg said, adding “The worst thing Chinese threat actors will see is their malware activity becoming public.”
“I encourage governments around the world to make attacks public,” he further added.
Thursday’s press conference was jointly addressed by Ahlberg and threat intelligence analyst Charity Wright. They spoke on issues of motivation, attribution, methodology, and modus operandi behind Red Echoe’s targeting of India’s critical assets.
China’s Cyber Operations to Continue in 2021
The 12 organisations that were targeted in 2020 are
- Power System Operation Corporation Ltd,
- NTPC Ltd
- NTPC Kudgi STPP,
- Western Regional Load Despatch Centre
- Southern Regional Load Despatch Centre
- North Eastern Regional Load Despatch Centre
- Eastern Regional Load Despatch Centre
- Telangana State Load Despatch Centre
- Delhi State Load Despatch Centre
- DTL Tikri Kalan (Mundka) of Delhi Transco Ltd
- V.O. Chidambaranar Port
- Mumbai Port Trust
As bilateral tensions continue to rise, “We expect to see a continued increase in cyber operations being conducted by China-linked groups such as RedEcho, in line with national strategic interests,” Recorded Future’s report stated.
Further, according to the report, China will likely also continue to exert influence over other nations, particularly those that are within the sphere of influence of their BRI investment programme, which may lead to more cyber operations aimed at furthering strategic advantage.
Ahlberg ruled out the possibility of the targeting being done to gain material advantage or for cyber espionage.
“Tageting of strategic Indian power grid assets provides limited economic espionage activities,” Ahlberg said.
According to him, the targeting poses “pre-positioning concerns”. This means the targeting was done to achieve network positioning in advance to gain some specific advanatages.
According to the company’s findings, this pre-positioning could have been done to:
- Intelligence gathering for future cyber activity
- Place destructive malware
- As a warning/show of force during heightened bilateral tensions
- Potential information operation to disturb Indian population